Cloudflare Post-Quantum Encryption for IPsec Is Now Generally Available
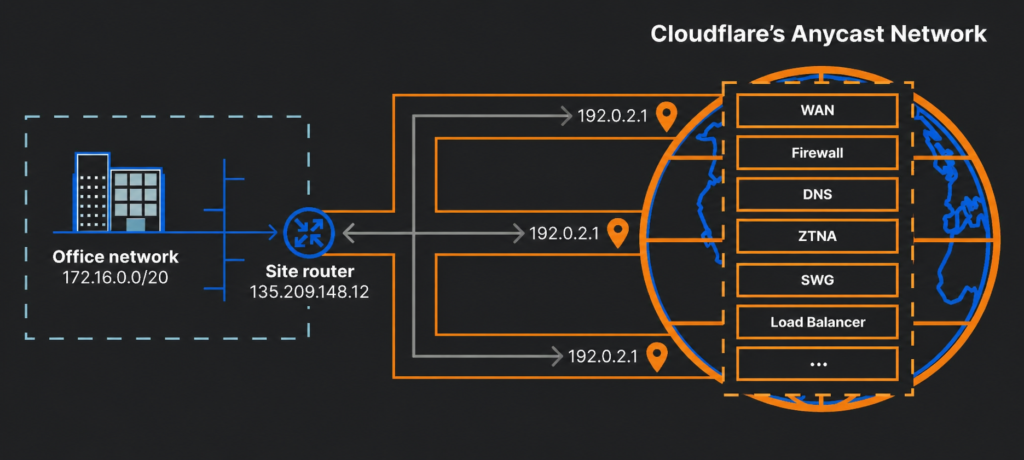
Cloudflare has officially made post-quantum encryption for IPsec generally available, closing a long-standing security gap in site-to-site networking. Businesses can now protect their wide-area networks against future quantum threats, using existing hardware from Cisco and Fortinet.
The move is part of Cloudflare’s broader push toward full post-quantum security by 2029, a deadline the company recently moved forward after new advances in quantum computing raised fresh urgency. The company confirmed interoperability with Fortinet FortiOS 7.6.6 and later and Cisco 8000 Series Secure Routers from version 26.1.1.
Post-quantum encryption for IPsec relies on hybrid ML-KEM, standardised as FIPS 203 by NIST. ML-KEM, short for Module-Lattice-Based Key-Encapsulation Mechanism, runs on standard processors. It needs no specialist hardware. It also authenticates both parties across the Internet, something older approaches like Quantum Key Distribution (QKD) cannot do on their own.
The new implementation follows draft-ietf-ipsecme-ikev2-mlkem, an IETF draft that specifies a hybrid handshake. In practice, a classical Diffie-Hellman exchange runs first. Its derived key then encrypts a second exchange using ML-KEM. The outputs of both are combined into the session keys that secure IPsec data traffic via the Encapsulating Security Payload protocol.
The threat driving this urgency is real. Harvest-now-decrypt-later attacks allow adversaries to collect encrypted data today and hold it until quantum computers are powerful enough to break classical encryption. As Q-Day draws closer, this risk is no longer theoretical. More than two-thirds of human-generated TLS traffic to Cloudflare’s network is already protected by hybrid ML-KEM. However, the IPsec world has lagged behind, until now.
The gap between TLS and IPsec is roughly four years. Cloudflare enabled post-quantum key agreement in TLS as far back as 2022, well before NIST finalised ML-KEM. The TLS community moved fast and converged on a single standard. IPsec, by contrast, spent years weighing QKD, a technology that requires a dedicated physical link and specialised hardware. Notably, the NSA, Germany’s BSI, and the UK’s NCSC have all warned against relying solely on QKD for post-quantum security.
The standard also fills a gap left by RFC 9370, published in 2023, which allowed multiple key exchanges in parallel but never specified which cipher suites to use. That ambiguity led some vendors to ship early, proprietary implementations, creating fragmentation. Cloudflare’s implementation, for instance, does not yet interoperate with Palo Alto Networks’ RFC 9370-based version, because it launched before draft-ietf-ipsecme-ikev2-mlkem was available. Cloudflare says it hopes to resolve that as the industry consolidates.
One challenge remains. Draft-ietf-ipsecme-ikev2-mlkem secures post-quantum encryption, but post-quantum authentication for IPsec is still being developed. That piece matters too, without it, live systems after Q-Day could still face attacks from quantum adversaries. Cloudflare is calling on the IPsec community to prioritise interoperable standards rather than divert focus to niche approaches like QKD.
Cloudflare IPsec connects data centres, branch offices, and cloud environments to Cloudflare’s global Anycast network. It supports site-to-site WAN, outbound Internet traffic, and connectivity to the Cloudflare One SASE platform. Post-quantum encryption for IPsec is available at no additional cost to customers, in line with the company’s stated position that post-quantum cryptography should be free.
For organisations running Cisco or Fortinet branch connectors, post-quantum protection for their WAN traffic is available today.